originally published February 4, 2012
Today’s article will remain on this site for roughly three and half hours, tops. By then, the hackers will have found it and destroyed it. They might go after my credit rating for good measure, but that would be akin to shooting a dead cow.
I came across a group of hackers (or a ‘hacker collective’, because that sounds cooler I guess) called Helith. The name comes from the German word for ‘Heroes’ because… well, I’ll quote the article directly:
“It was chosen because the group believes that nobody cares for those who are poor or those who did not had the same chances like studied hackers.”
From that sentence, it would appear that Helith is made up of semi-literate Robin Hoods, striving to provide economic balance to the masses. Let’s check out a few of the projects they’ve been involved in.
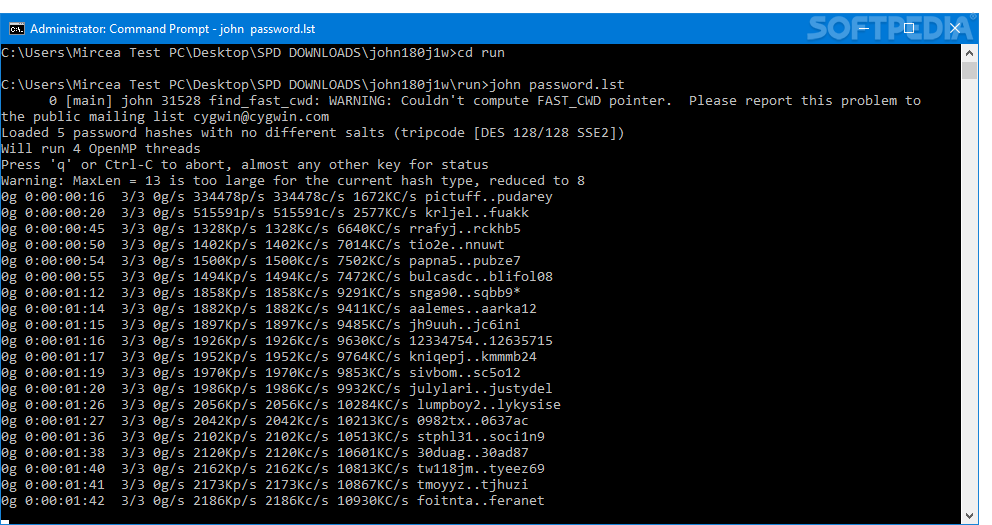
John the Ripper is a free program for cracking passwords. I checked out the program’s site, and from what I can gather this program is intended to level the economic playing field by allowing poorer people to access expensive programs through made-up passwords. I could be mistaken, but encouraging copyright violations seems a little less noble than subversive.
Helith has worked on the Metasploit project as well. Metasploit is a piece of software specifically for taking advantages of security vulnerabilities and allowing hackers access to remote servers. There is value in software like this of course – if used by a company against their own servers, they can patch up any weaknesses in their system. If only the Empire had used Metasploit, they might have clued into that womprat-size opening on the first Death Star.
Some hackers arguably use the information they get from network scanners and password crackers for good, just to let folks know what they have to fix. And as far as I can tell, Helith doesn’t have a reputation of evil-doings.
That’s not to say their hands are completely clean though. In 2007, the group reportedly hacked into the Deutsche Bank’s servers and, to prove their feat, posted the company’s entire email database to BitTorrent, allowing anyone in the world to download it. Needless to say, the bank’s employees were likely deluged with pleas for help by various Nigerian princes that year.
Their website insists that Helith’s only real intent is to exchange knowledge, not to cause any panic or ID-theft fiascos. There are no new updates since May of 2010, so who knows what Helith is up to now?
Other hacker collectives aren’t quite so chaste in their ideology. Also, they have fantastically bizarre names. Let’s check a few out, so that they can Google themselves and find this page, hopefully not replacing every picture with a jpeg of Donny Most.
The Honker Union, which sounds like a collective of Vaudevillian performers, is a Chinese hacker group that was founded in the wake of the (accidental) NATO bombing of the Chinese Embassy in Belgrade. These nationalists have taken their cyber-war to American websites and anyone else who is on the outs with the Chinese. This sounds perfectly rational, because impersonating Tibetan dissenter and blogger Tsering Woeser in order to… I don’t know, accidentally give her a bunch of publicity? Yeah, that’s a good way to stick it to the Yanks.
On the more admirable side of the hacking world (and I use this term with a giant asterisk:

…because I don’t know how many rotten things this group may have done as well), we have Genocide2600. I’ve heard of these guys. This group’s fifteen minutes of press came when they joined forces with numerous law enforcement communities to go after child pornography on AOL in the 1990s. Anyone who busts pedophiles is downright heroic in my book… these guys should have grabbed the name ‘Helith’.
The Phone Losers of America is a phreaking group. Phreaking, for those who aren’t in the know (I had to look it up, but then I have to look almost everything up) is a form of phone-hackery, originally used to bypass being charged for making calls. The history of phreaking is actually pretty interesting.
In 1957, Joe Engressia, a blind kid, discovered that if he whistled the fourth E above middle C (2600 Hz – there’s that number again), his phone line would reset. When a phone line resets, the phone company thinks the call is over, even if it isn’t. This leaves you free to keep talking for free, which was a big deal before Voice-Over-IP technology made it possible for us modern folk to chat for free.
There’s a famous story about a whistle that came bundled with Cap’n Crunch cereal for a while. The whistle happened to blow right at that frequency. On some phone systems, you could use this freebie whistle to reset the line, then dial the numbers to call Uganda and chat all day (or as long as you can find things to talk about with a Ugandan).
The Phone Losers of America appear to be best known for their prank calls now, which can be heard by the masses through their irregularly broadcast podcasts.
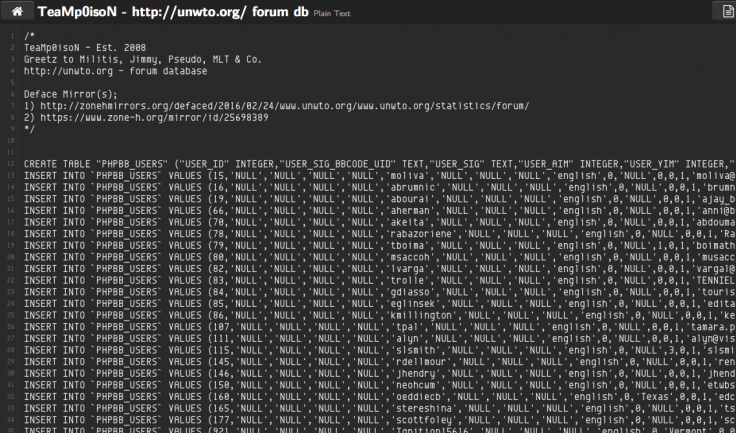
TeaMp0isoN is another snippet of the evil hacking world, one which I’d just as soon not piss off. They have targeted the UN, Facebook, NASA, the Israeli government, Barack Obama, Tony Blair, and Sean Combs. Wait… P-Diddy? Alright, I’m not going to argue, these guys could probably disintegrate a little website like mine, so I’m sure they’re all handsome and large-penissed (except the women, whom I’m certain are exquisite).
Let’s check out one more of these groups: the Gay Nigger Association of America. Jesus, really?
This is a group of online trolls. Again, for those who don’t know what this is, trolling is another way of simply pissing people off. The GNAA uses ‘crapflooding’, which attacks blogs, flooding comments pages with a bunch of repeated words and phrases. They also found a way to convince CNN reporter Paula Zahn that one in three Americans believed that 9/11 was carried out by Israeli agents. This is not a group of Robin Hood hackers – these guys want people to be pissed off.
Hacking will never go away, but it does provide us, the viewers, with a little bit of entertainment. Hopefully the best hackers are using their skills for good, to defend our most essential online homes from their evil counterparts. If not, it’s entirely possible we’ll wake up tomorrow morning and find all our Facebook photos have been replaced with pictures of dicks.